Looking into the 2016 Operational Risk Management (ORM) rear view
mirror, you may be asking yourself several questions. How many
significant losses have occurred this past year, from the failed people,
processes, systems or external events in your organization?
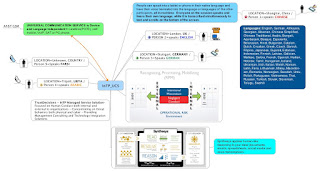
You could be asking your team why you have yet to become the target of our adversaries also known as COZYBEAR, APT28 or APT29, CloudDuke, or even Energetic Bear. If you don't know who these are, then you probably already are "owned" by this adversary. It may finally be a priority, to become a participant in the "Automated Indicator Sharing" (AIS) initiative.
Where are you navigating to in 2017?
As we look across the vast landscape of our rapidly changing business and government domains, there is no turning back. There is no ability to retreat or to acquiesce, in a world so full of continuous Operational Risk.
There is no certainty. There is no true assurance. There is only the ability to solve problems faster than your adversary or competition. Some may call this resilience.
Therefore, the direction you take will forever shape your continued exposure to risks and your strategy for opportunities, that you do have control over. It is a choice and the questions by the Board of Directors, the Plaintiff Bar or the U.S. Attorney, are not going to be the most difficult ones to answer.
In 2017, any major influential organization will be getting more transparent. The metrics and the formulas (think mathematical algorithms) for counting and creating wealth will be further disclosed, the rules will change faster and more transparently. Buyers and Sellers of digital content and intelligence, will increase their levels of "Digital Trust".
How will these parties, partners and participants in a vast and exponentially expanding ocean of digital rules become more trustworthy? They will begin to better understand the DNA of their respective TrustDecisions.
The constituents of organizations, countries and ICT (Information, Communications & Technology) entities will finally realize that transparency of the rules is a vital step to trustworthiness. Better understanding the "Rules for Composing Rules" is a place to start. Jeffrey Ritter is the visionary on this topic:
To survive the journey to your intended destination in 2017, will require bold new thinking. It will be necessary to make many sacrifices along the way, to your intended destination. On the ground, or in a virtual domain. The solution-sets that you utilize, will require new entities (change agents) to be even more effective in solving problems that arise.
These new entities (human and digital), that will solve problems more efficiently and effectively with you, are ready now. So what will you do next to adopt, embrace, espouse, endure, tolerate, and even endure the journey ahead?
May your exploration and travels in 2017 produce the intended outcomes. We wish you a productive and Happy New Year!
You could be asking your team why you have yet to become the target of our adversaries also known as COZYBEAR, APT28 or APT29, CloudDuke, or even Energetic Bear. If you don't know who these are, then you probably already are "owned" by this adversary. It may finally be a priority, to become a participant in the "Automated Indicator Sharing" (AIS) initiative.
Where are you navigating to in 2017?
As we look across the vast landscape of our rapidly changing business and government domains, there is no turning back. There is no ability to retreat or to acquiesce, in a world so full of continuous Operational Risk.
There is no certainty. There is no true assurance. There is only the ability to solve problems faster than your adversary or competition. Some may call this resilience.
Therefore, the direction you take will forever shape your continued exposure to risks and your strategy for opportunities, that you do have control over. It is a choice and the questions by the Board of Directors, the Plaintiff Bar or the U.S. Attorney, are not going to be the most difficult ones to answer.
In 2017, any major influential organization will be getting more transparent. The metrics and the formulas (think mathematical algorithms) for counting and creating wealth will be further disclosed, the rules will change faster and more transparently. Buyers and Sellers of digital content and intelligence, will increase their levels of "Digital Trust".
How will these parties, partners and participants in a vast and exponentially expanding ocean of digital rules become more trustworthy? They will begin to better understand the DNA of their respective TrustDecisions.
The constituents of organizations, countries and ICT (Information, Communications & Technology) entities will finally realize that transparency of the rules is a vital step to trustworthiness. Better understanding the "Rules for Composing Rules" is a place to start. Jeffrey Ritter is the visionary on this topic:
To be part of the disruption, any business must look in two directions—toward the companies that supply digital information to them, and toward the companies with whom their own digital assets are shared. To succeed in creating wealth, and enriching the trust that exists throughout a company’s ecosystem, companies must evaluate how they can be more transparent with their information suppliers, and what levels of transparency to demand from those companies who are outbound recipients. What are the right metrics to show how data or content (like videos) are performing? How will the reporting occur? Are the economic exchanges properly balanced by the value of the data being shared?The negotiations have been in progress for days, months and years. The question remains; where are you navigating to in 2017 and beyond? What resources will you require to get you to your planned destination? How will you adapt along the way, as the environment you are operating in changes?
To survive the journey to your intended destination in 2017, will require bold new thinking. It will be necessary to make many sacrifices along the way, to your intended destination. On the ground, or in a virtual domain. The solution-sets that you utilize, will require new entities (change agents) to be even more effective in solving problems that arise.
These new entities (human and digital), that will solve problems more efficiently and effectively with you, are ready now. So what will you do next to adopt, embrace, espouse, endure, tolerate, and even endure the journey ahead?
May your exploration and travels in 2017 produce the intended outcomes. We wish you a productive and Happy New Year!